HyperSphere
SecureStorage™
This is what encryption was meant to be: No persistent keys to manage or steal. Security that outsmarts AI and quantum threats. Data protection that just works.
This is what encryption was meant to be: No persistent keys to manage or steal. Security that outsmarts AI and quantum threats. Data protection that just works.
With a traditional KMS, your data is only as safe as the key that protects it. If an attacker gets a key—through any means—they can decrypt everything encrypted under it. And if someone breaches your S3 bucket directly, the only thing standing between them and your data is that key.
Manual rotations, HSM maintenance, access policy auditing, cross-region replication, emergency key compromise response. Key management eats up precious engineering resources. And a single misconfiguration can leave data unrecoverable—or silently exposed.
Nation-state actors are exfiltrating traditionally encrypted data today, stockpiling it for future decryption by quantum computers. It takes years to migrate an entire KMS to post-quantum algorithms, and most organizations haven't even started yet. Until then, you're exposed.
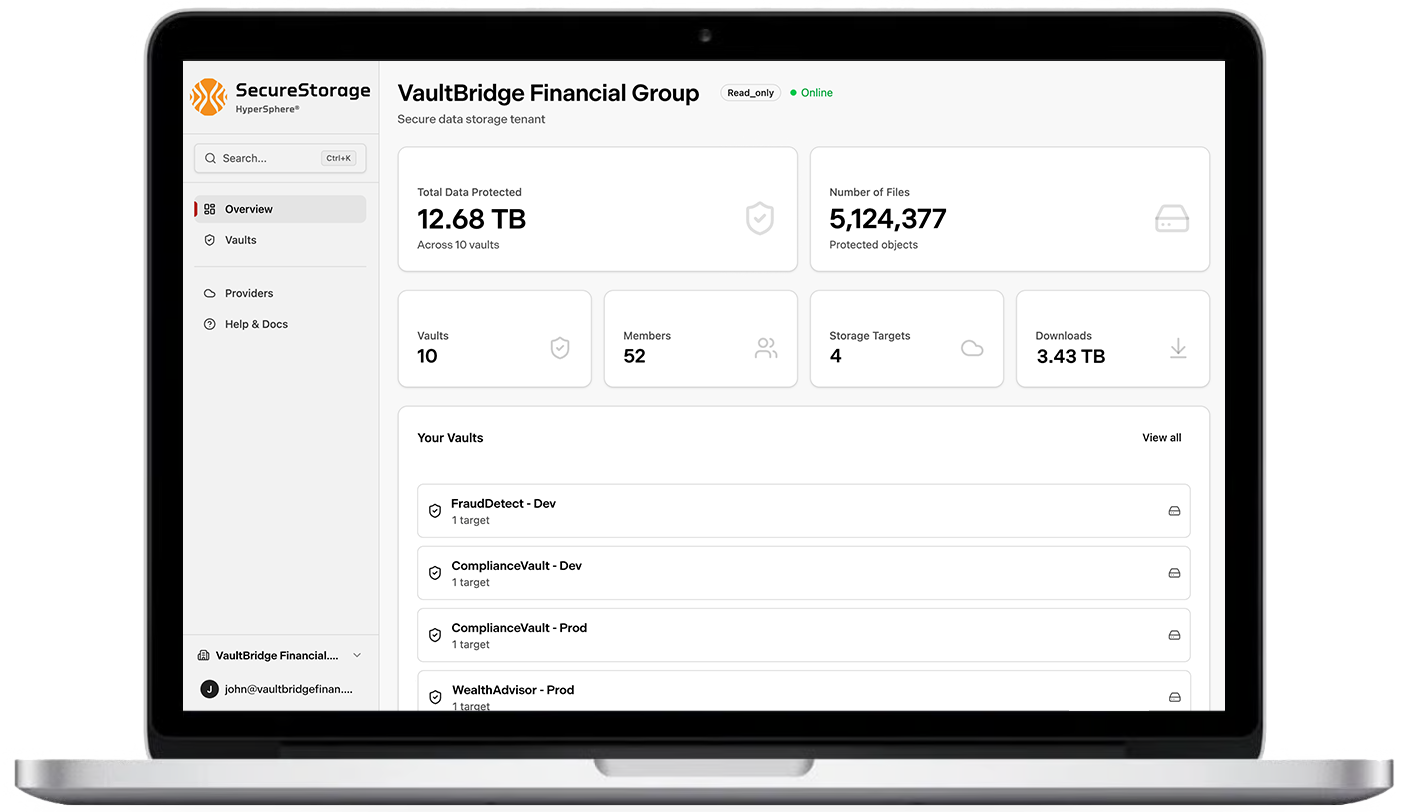
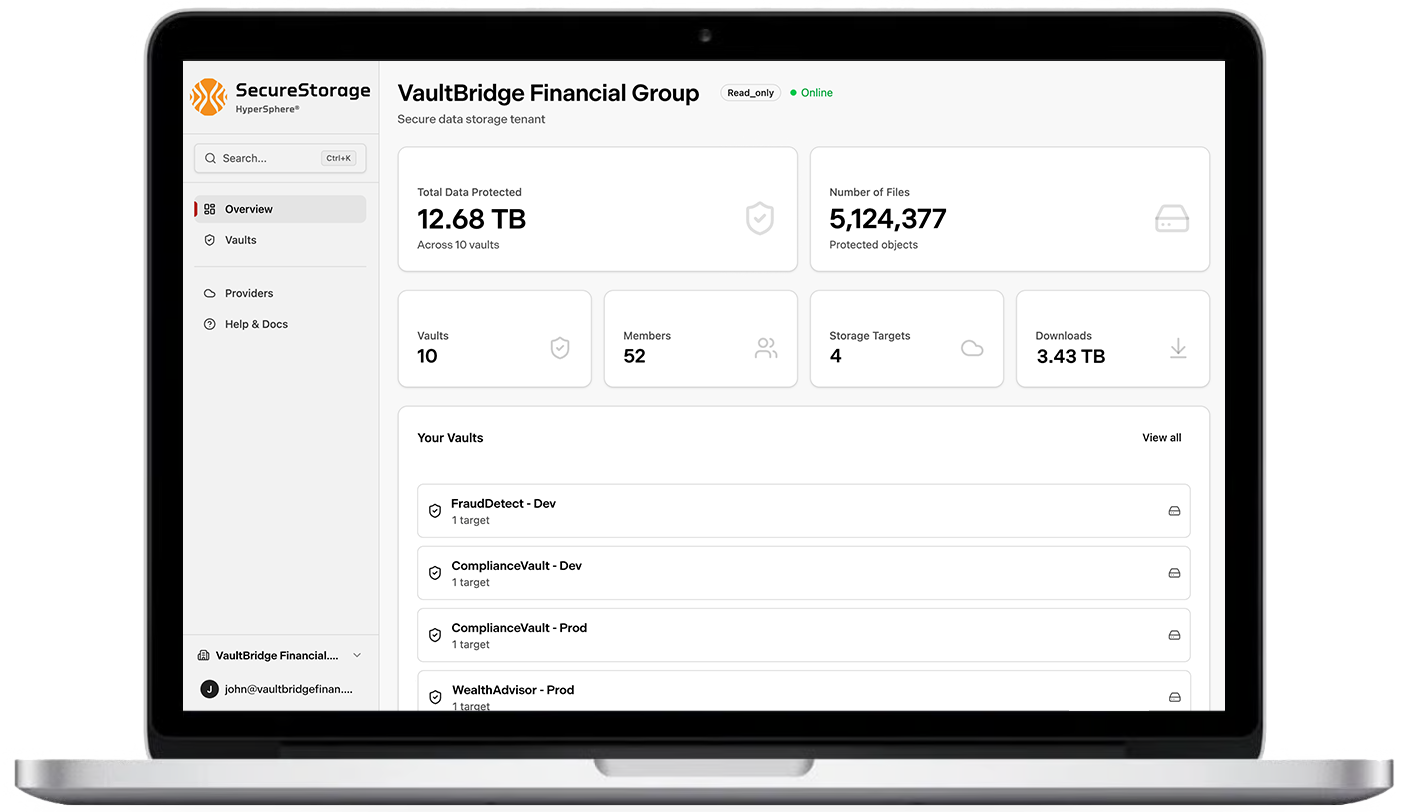
HyperSphere SecureStorage encrypts unstructured data at rest without relying on stored keys or key management systems (KMS).
With HyperSphere SecureStorage, encryption keys are never stored on disk, in databases, or in any key management service. They're dynamically derived and destroyed when no longer needed. No human has to generate, rotate, back up, or manage any key—ever.
SecureStorage doesn't rely on the type of encryption that quantum computers are expected to break. Our unique methodology uses NIST-recognized, post-quantum-computing (PQC) algorithms to secure data for decades to come. This isn't a roadmap promise. It's how the product works today.
SecureStorage deploys within hours from the AWS Marketplace in on-prem, edge, or cloud environments. The entire key management operational surface vanishes—no manual processes or KMS clutter. Users store and access data as they always have. Data protection just happens.
The standard response to the quantum threat is a multi-year post-quantum cryptography (PQC) migration — new algorithms, new key hierarchies, new integration testing, new risk windows.
SecureStorage sidesteps the entire problem. Because no public-key cryptography exists in the critical path, there is nothing to migrate. Protection is quantum-resistant from day one — architecturally, not algorithmically.
Every month of inaction is another month of quantum-vulnerable key wrapping and "harvest now, decrypt later" exposure.
Breaks the public-key cryptography that protects master keys in every traditional KMS. Renders key hierarchies exposed.
SecureStorage: No public-key crypto in critical pathProvides only quadratic speedup against AES-256. Still computationally infeasible—would require more energy than exists in the observable universe.
SecureStorage: AES-256-GCM per piece, distributed protectionAdversaries exfiltrate encrypted data today, stockpiling it for future quantum decryption. Data with 10+ year sensitivity windows is already at risk.
Traditional KMS: Exposed until PQC migration completesSecureStorage encrypts data without storing keys on disk or in any external service. There's no manual key management or KMS needed, and no rotation schedule to maintain. If storage is breached, attackers get nothing usable.
Protection is quantum-resistant and enforced architecturally—not by access policies, admin privileges, or trust in a provider. A misconfigured bucket or a compromised machine can't bypass what's mathematically enforced.
SecureStorage is designed to "fail closed." When something goes wrong—compromised storage, stolen credentials, infrastructure breach—the system denies access to protected data rather than exposing it.
SecureStorage protects data in any S3-compatible storage. It works with your existing applications, SDKs, and CLI tools—no code changes needed. Deploys from the AWS Marketplace in minutes.
Protect data across cloud and on-prem environments simultaneously. Distribute protection across regions, providers, and jurisdictions without managing a separate KMS for each.
Every access attempt and operation is logged automatically. Generate compliance evidence in hours, not weeks—with built-in support for FIPS 140-3, CMMC, HIPAA, GDPR, and ITAR/EAR requirements.
Classified and controlled unclassified information (CUI) requiring long-term protection against quantum threats. SecureStorage enables "encrypt now, secure forever" for data that must remain confidential for decades.
Transaction records, customer PII, and trading algorithms that represent both competitive advantage and regulatory liability. Eliminate key custody risk for data under evolving DORA and NIST mandates.
Electronic health records and genomic data requiring protection that scales beyond individual patient lifetimes. HIPAA-compliant encryption that remains effective as computational threats evolve.
Research data, product designs, and strategic plans that represent core competitive advantage. Protection that requires compromise of multiple geographic locations and organizational boundaries.
See how SecureStorage eliminates key management entirely while delivering the strongest data protection against quantum threats.