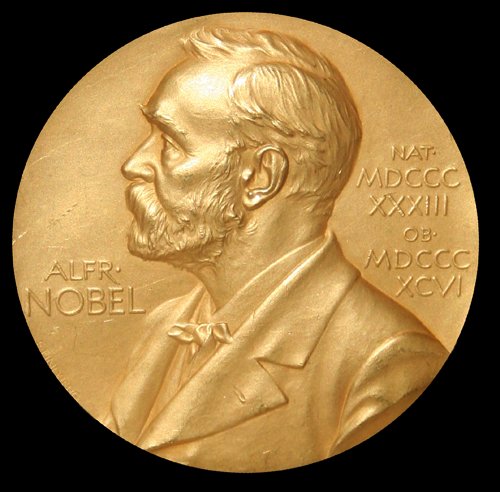
Copenhagen, 1940. Nazi forces had just invaded Denmark, and in the basement laboratory of the Niels Bohr Institute, chemist George de Hevesy faced an impossible problem. Two Nobel Prize gold medals—belonging to German physicists Max von Laue and James Franck—sat on his desk, and the Gestapo was coming.
These weren't just valuable objects. They were symbols. Von Laue and Franck had sent their medals to Denmark for safekeeping specifically because of their opposition to the Nazi regime. If discovered, the medals would not only be confiscated—they would be used as propaganda, and their owners would face severe consequences.
De Hevesy couldn't hide them. Nazi officials were methodically searching the institute, and gold medals were exactly the kind of asset they were hunting for. He couldn't smuggle them out—Denmark was under occupation, borders were closed, and any attempt to move such valuable items would be immediately detected.
The Invisible Solution
So de Hevesy did something remarkable: he dissolved them.
Using aqua regia—a mixture of nitric and hydrochloric acid so corrosive it can dissolve gold—he transformed the solid medals into an orange solution. Then he placed the beaker on a shelf in his laboratory, amid dozens of other beakers containing various chemical solutions. The medals were now invisible, hiding in plain sight.
"The solution was disguised as something completely ordinary. The Nazis searched the lab multiple times, but they never noticed the beaker. They were looking for gold medals—not an unmarked jar of liquid." — Account from the Niels Bohr Institute archives
The German occupation forces did search the institute. They ransacked offices, interrogated staff, and inventoried assets. But they walked right past the beaker containing 350 grams of dissolved gold. It wasn't encrypted. It wasn't locked in a vault. It was transformed into something that appeared worthless.
Timeline of Events
Max von Laue and James Franck, German physicists in exile, send their Nobel Prize gold medals to Denmark for safekeeping at the Niels Bohr Institute
Nazi Germany invades Denmark. The institute becomes vulnerable to search and confiscation
George de Hevesy dissolves the medals in aqua regia, leaving them on a shelf as an unlabeled orange solution
German forces search the institute multiple times. The solution remains undiscovered on the laboratory shelf
After the war, de Hevesy precipitates the gold from the solution and sends it to the Royal Swedish Academy of Sciences, where new medals are cast and returned to von Laue and Franck
The Strategic Brilliance
What makes this story remarkable isn't the chemistry—aqua regia's ability to dissolve gold had been known since the Middle Ages. What's remarkable is the strategic thinking.
De Hevesy understood a fundamental principle: security isn't just about hiding things. It's about removing their value to an adversary. The Nazis weren't looking for beakers of orange liquid. They were looking for gold medals. By transforming the form while preserving the substance, de Hevesy made the medals simultaneously present and impossible to find.
The Chemistry of Protection
Aqua regia (Latin: "royal water") is a 3:1 mixture of hydrochloric and nitric acid. It can dissolve noble metals like gold and platinum that resist other acids. The dissolution is reversible—gold can be precipitated back out of solution by neutralizing the acid and adding a reducing agent. Nothing is lost; only the form changes.
Three Layers of Strategic Defense
1. Transformation, not concealment. Traditional hiding places—safes, false walls, buried containers—all share a vulnerability: if found, they immediately reveal their contents. De Hevesy's approach was different. Even if discovered, the beaker revealed nothing of value. The gold was there, but unrecognizable.
2. Hiding in plain sight. The most secure location wasn't a hidden vault. It was a laboratory shelf, surrounded by dozens of similar beakers. Any attempt to test every solution in the building would take months and destroy the institute's work. The protection wasn't in obscurity—it was in making the target indistinguishable from everything around it.
3. Reversibility without dependency. The gold could be recovered, but only by someone with specific knowledge. There was no key to steal, no safe to crack, no single point of failure. The "protection mechanism" was knowledge itself—distributed, unable to be captured.
What the Story Teaches Us
Eighty-five years later, we face an analogous challenge. Instead of gold medals, we're protecting data. Instead of Nazi searchers, we face credential theft, insider threats, and AI-accelerated attacks. The form changes, but the strategic question remains the same:
How do you protect something of value when the adversary has access to where it's stored?
The traditional answer has been to build better locks. Stronger encryption. More complex key management. Sophisticated access controls. But this approach assumes that if an adversary reaches your storage—if they get credentials, compromise a server, or gain physical access—they can extract value.
De Hevesy's approach suggests a different answer: make the stored form unusable to anyone who doesn't possess specific reconstruction capability. Transform the asset so that possession without proper authority yields nothing.
The Modern Parallel: Keyless Data Protection
Today's enterprise data faces the same threat the Nobel medals faced in 1940: authorized access paths being used by unauthorized actors. Credentials are compromised. Cloud storage is misconfigured. Insider threats are real. The question isn't if your storage will be accessed—it's whether that access yields usable information.
Threat: Authorized searchers (German forces with legal access to Danish facilities) looking for valuable assets
Solution: Transform medals into chemical solution—present but non-reconstructable without specific knowledge
Result: Multiple searches over 5 years, zero discoveries
Threat: Authorized access (compromised credentials, insider threats, misconfigurations) used to exfiltrate valuable data
Solution: Transform data into non-reconstructable state—present in storage but unusable without proper quorum
Result: Credential compromise doesn't yield usable data exfiltration
Beyond Metaphor: Architectural Lessons
The Nobel medal story isn't just a historical curiosity—it's a design pattern. When we examine what made de Hevesy's approach successful, we find principles that translate directly to modern data protection:
Principle 1: Security through transformation. Don't just encrypt data; transform it into a state where standard reconstruction methods fail. The attackers know the data exists. They may even access the storage. But what they access must be fundamentally different from what they seek.
Principle 2: No persistent reconstruction path. De Hevesy didn't write down the formula for reversing the process. He didn't create a "key" that could be stolen. The knowledge to reconstruct existed only in distributed form—his understanding of chemistry, the context of the war, the specific procedures. Similarly, modern protection should eliminate persistent keys that create single points of failure.
Principle 3: Operational continuity. The medals were protected, but they weren't locked away in a remote location that would make them inaccessible. They remained at the institute where they could be monitored and, when safe, recovered. Protection shouldn't mean isolation—it should mean selective access under controlled conditions.
The Epilogue
In 1945, after Denmark's liberation, de Hevesy returned to his laboratory. The beaker was still there, untouched. He precipitated the gold from the solution, dried it, and sent the recovered metal to the Royal Swedish Academy of Sciences. New medals were cast from the original gold and returned to von Laue and Franck.
The metals survived. The symbols survived. And critically, the protection method never depended on the adversary remaining ignorant of what had been done. Even if the Nazis had known that gold was dissolved somewhere in the building, finding it among thousands of chemical samples would have been impossible without destroying the institute's scientific work entirely.
This is the ultimate test of security architecture: it must remain effective even when the adversary understands the mechanism.
Conclusion: The Gold Standard
De Hevesy's story endures not because it's a clever trick, but because it exemplifies strategic thinking about protection. When traditional security measures—hiding, locking, guarding—were insufficient, he asked a different question: What if the asset were present but unusable?
Today, as enterprises face credential compromise, cloud misconfigurations, and AI-accelerated attacks, that question is more relevant than ever. The answer isn't bigger locks. It's transformation. It's removing the reconstruction path from the storage itself. It's making the difference between having access to data and having usable data as wide as the difference between a beaker of orange liquid and a gold medal.
The medals survived because they were there, but not there. Present, but transformed. Accessible to everyone, usable by no one except those with the proper capability to reconstruct.
That's not just good chemistry. It's the architecture of strategic protection.
How HyperSphere Applies These Principles
HyperSphere's zero-management architecture embodies de Hevesy's approach: data is transformed into a non-reconstructable state at rest. Valid credentials and cloud access don't yield usable information. Like the dissolved medals, the data is present in storage but requires proper reconstruction capability—not a stored key—to restore. Even if an adversary understands the system, stolen storage yields nothing operational.